Necurs Returning After a Short Vacation
Blog
Thought Leadership
Necurs Returning After a Short Vacation
Jonathan French
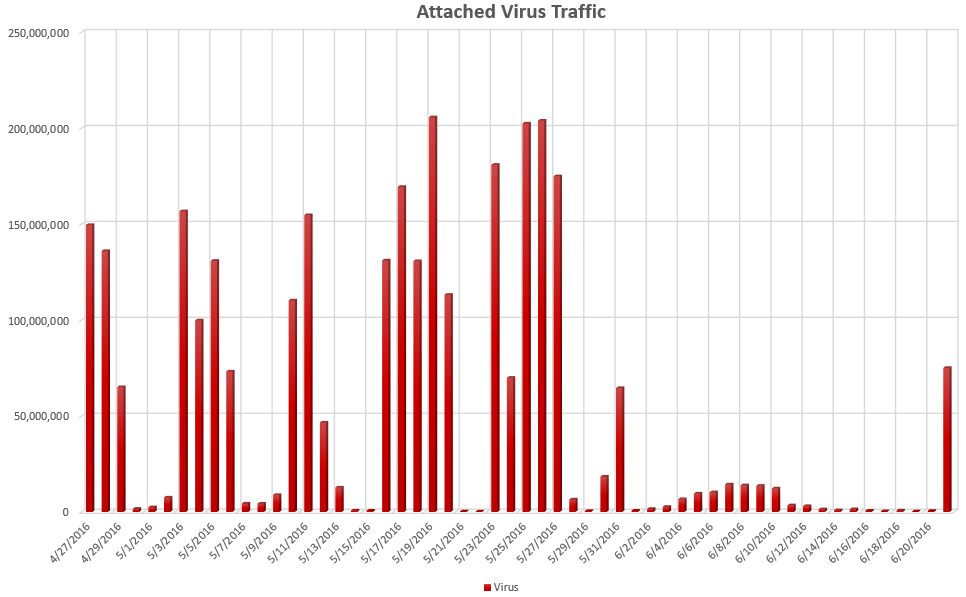
Virus traffic has been huge so far in 2016. Mostly, this has been thanks to ransomware, and in particular, Locky distributed by the Necurs botnet. We've been seeing malware traffic counts in the tens of millions daily here for sometime now. This, of course, has its ups and downs, but for the past three weeks it's been almost entirely downs. The past three weeks have been ranging from around 3-10 million malicious attachments a day which has been a significant decrease in the previous months' traffic. However, around noon today, we noticed a sharp increase in virus traffic once again.
In a few hours since steady malware started coming in, we're at a little over 80 million for the day so far. This is likely related to what other organizations have been seeing in regards to the Necurs botnet essentially going offline around June 1st. Necurs has been blamed for the huge volumes in Locky and Dridex related malware this year. The botnet wasn't taken down earlier this month, but randomly stopped performing its nefarious control of infected computers. With the Locky campaigns today being very similar to what we've seen before, it looks like Necurs is coming back and ramping up. Whether or not this is a temporary spike or a return to pre-June 1 "normalcy" is too early to tell.
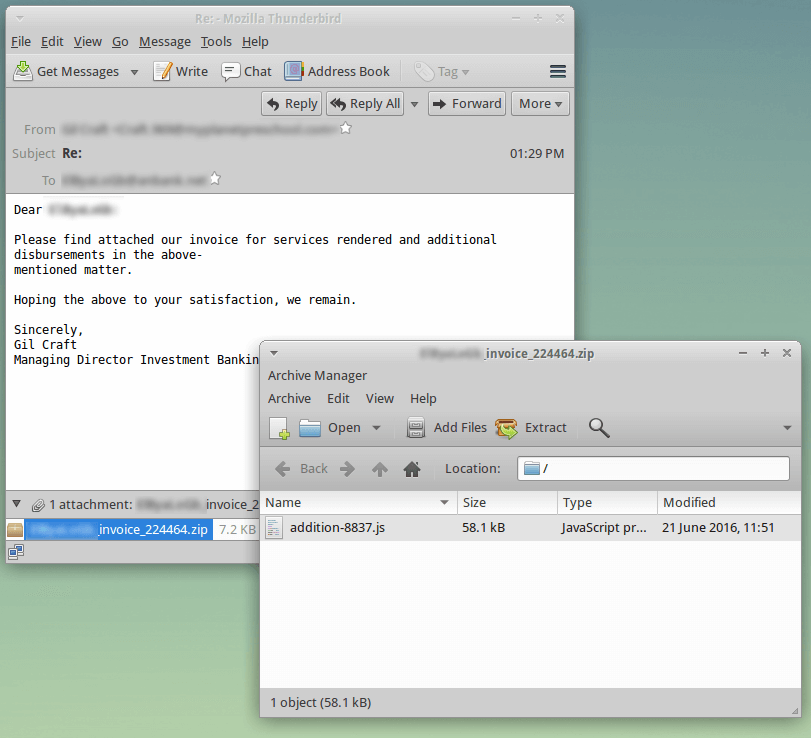
As for the campaign itself, there are multiple different .js files coming in with most just being slight variations in format. The few I checked on VirusTotal had a 2/54 hit for them, so not many AV providers are catching the file itself (though they may trigger upon execution or other actions the malware takes). So far, the malware traffic accounting for this spike has been handled by rules added anywhere from one-three months ago. Some of these matches were because the .js malware is so similar to previous campaigns, and other rules added a few months ago are just now hitting today. Trying to stay ahead of malware and planning for future variations pays off where sometimes entire campaigns can be stopped at the first message in situations like this. But as always, while we're keeping a close eye on the traffic and monitoring for any new variations or changes, our SecureTide customers remain protected.