Phishing campaigns spoof Citizens Bank, Wells Fargo
Blog
Thought Leadership
Phishing campaigns spoof Citizens Bank, Wells Fargo
Bear Huddleston

Recently AppRiver's Email Security filters have seen a flood of phishing campaigns using Wells Fargo and Citizens Bank templates.
The attacker's goal is to intercept the user's bank login information, and we all know what that could lead to - financial devastation.
From a previous article we did on phishing, Spotify Phishing Campaign Making the Rounds, we discussed how to spot a phishing email. One of the indications was the From Address stating the email was from the official domain. In the samples below, you will see that the From Address has been spoofed in an attempt to trick the recipient into believing they are receiving an email from an official organization or person.
Here is one of the samples AppRiver intercepted:
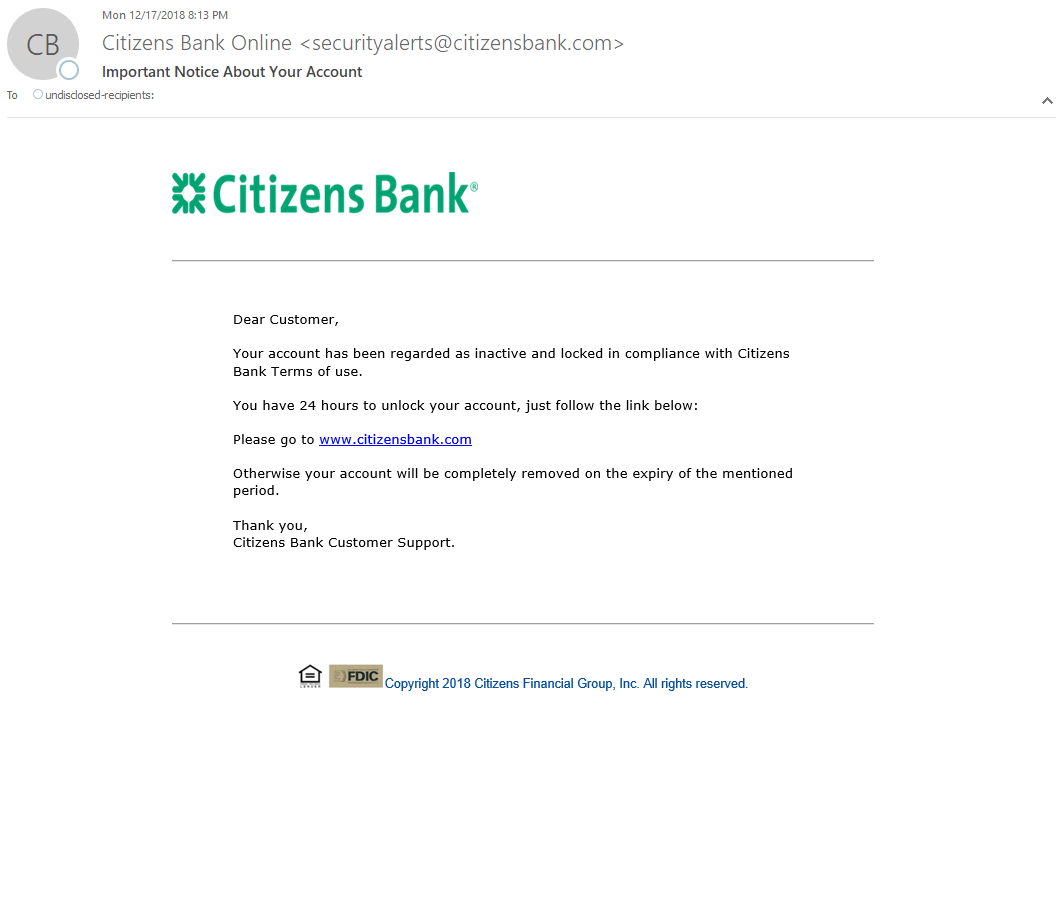
At first glance, this email appears to be from Citizens Bank, even the From Address says "citizensbank.com," which is an official domain for the banking institution. Because of that, the From Address would probably not raise any red flags.
However, let's look at the To Address. RED FLAG! In the sample provided, the attacker used "undisclosed-recipients," which means the email was sent to many people and the email addresses were undisclosed. This tactic is quite common in large phishing campaigns. It is important to note that legitimate bank institutions always will use a recipient's name in the To Address.
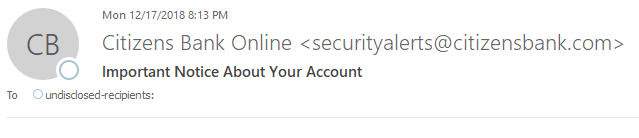
If the To Address doesn't cause pause, let's take a look at the hyperlink within the message. The email informs the recipient that their account is locked, and instructs the recipient to visit "www.citizensbank.com" to resolve the issues. Sure it looks legit, but if you hover your mouse over the link, the actual URL shows it most certainly is not going to Citizens Bank but instead to a deceptive website. That deceptive website will surely ask you for your username and password for Citizens Bank - giving the malicious actor exactly what he is hoping for.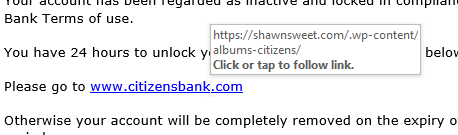
WELLS FARGO PHISHING CAMPAIGN
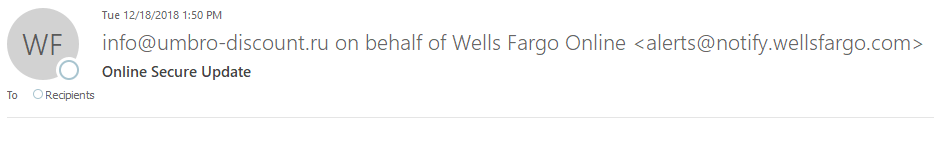
Let's take a look at the Wells Fargo phishing campaign. As you can see, it is very similar to the Citizens Bank scam.
 If we just look at the From Address, it appears to be wellsfargo.com. But this email is saying it was sent on BEHALF of Wells Fargo. Banking institutions do not send emails on behalf of themselves.Next up, the To Address, similar to the Citizens Bank email, shows "recipients" instead of the users' email addresses.Remember, this is an indication the scammer sent these emails in bulk, phishing for a bite.
If we just look at the From Address, it appears to be wellsfargo.com. But this email is saying it was sent on BEHALF of Wells Fargo. Banking institutions do not send emails on behalf of themselves.Next up, the To Address, similar to the Citizens Bank email, shows "recipients" instead of the users' email addresses.Remember, this is an indication the scammer sent these emails in bulk, phishing for a bite.
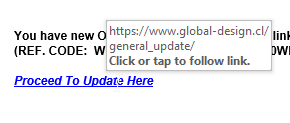
Just like the Citizens Bank phishing campaign, the payload is a link that will redirect you to a deceptive website that asks for your bank credential.
FALLING FOR IT FALL OUTIf these scammers get a hold of your bank login information, it goes without saying it could cause you serious financial damage. Once inside your account, the attackers have the ability to transfer money and gain access to more personal information.
If your bank account has been hacked by this or any method, call your bank immediately. Your bank will help mitigate the damage as much possible.
As an account holder, you should enable multi-factor authentication (MFA) - assuming your bank offers it - to help thwart a cybercriminal from gaining access to your money.
Multi-factor authentication will provide an extra step for you to gain access to your account. Typically with MFA, you will be prompted for a second credential that is sent via your preferred method (text, email or call). Once you enter in the code, you gain access to your account. Though MFA is not foolproof, it can slow down a scammer and hopefully help you avoid losing money.
MORAL OF THE STORYAs mentioned, always make it a best practice to check the URLs in every email message you receive - no matter how legitimate they look. When in doubt, don't click on anything within the message - or, if you have suspicions from the beginning, do not open the email..
If you are an AppRiver customer, forward the email to spam@appriver.com and our 24/7 trained cybersecurity specialists will review the email for your safety.
