Spoofed Navy Federal emails with PDF's linking to Phishing site
Blog
Thought Leadership
Spoofed Navy Federal emails with PDF's linking to Phishing site
Jonathan French
PDF phishing emails seem to be popular these days. While the PDF format isn't immune to its own vulnerabilities used for malware, the biggest abuse we see is a phishing link embedded in the PDF leading to an external site. With the popularity of PDF files in general and the fact you can embed links in them, it makes sense attackers would try to use this to their advantage. This use of PDF's for phishing usually comes in two flavors as well. It's either phishing for bank details, or for generic email login credentials.
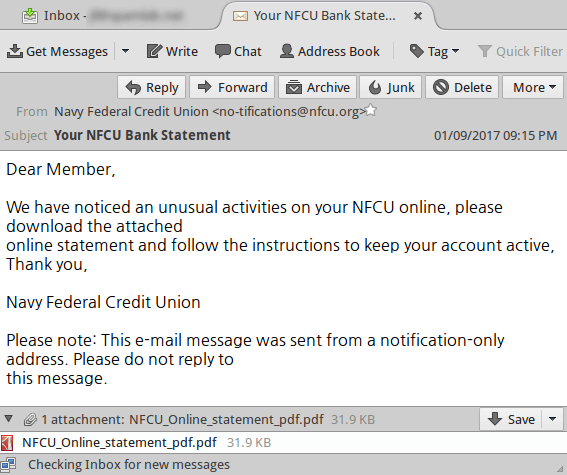
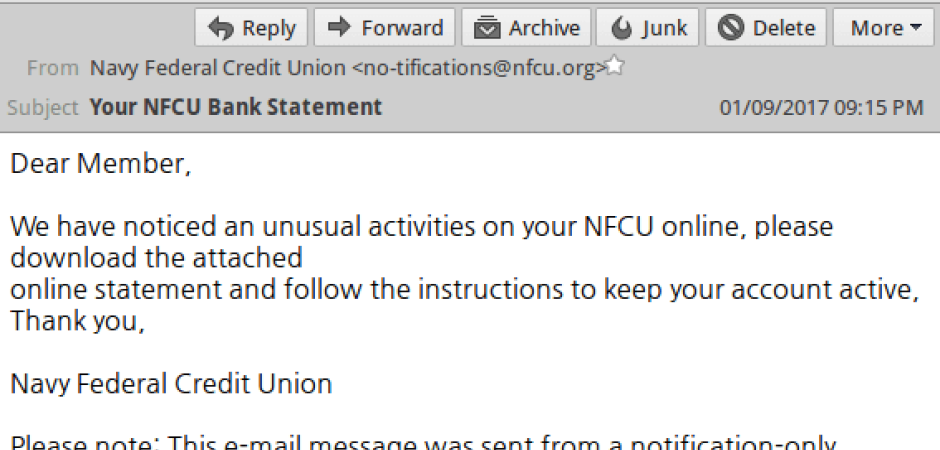
The below phishing email came in claiming to be from Navy Federal, the worlds largest credit union. It contained just a quick note about unusual activity and a PDF attached.
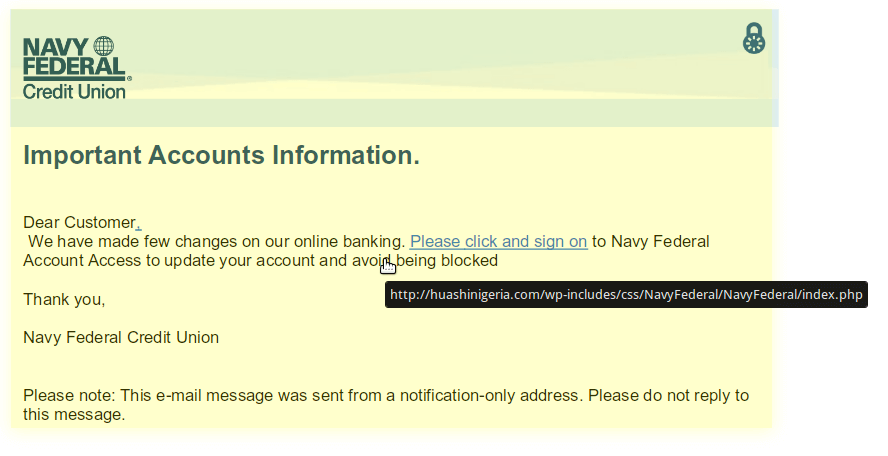
Opening up the attached PDF file, you get a small description of why you should click the link. An astute observer may notice it actually links to a compromised Wordpress site hosting the fake login page.
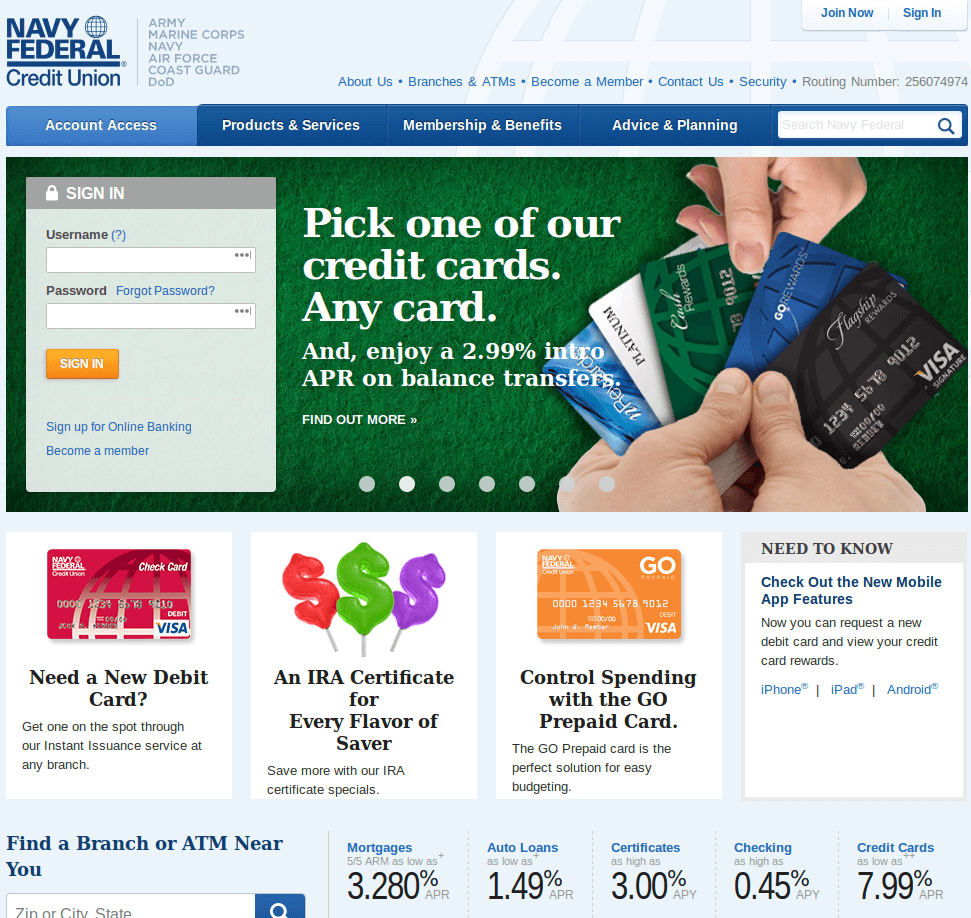
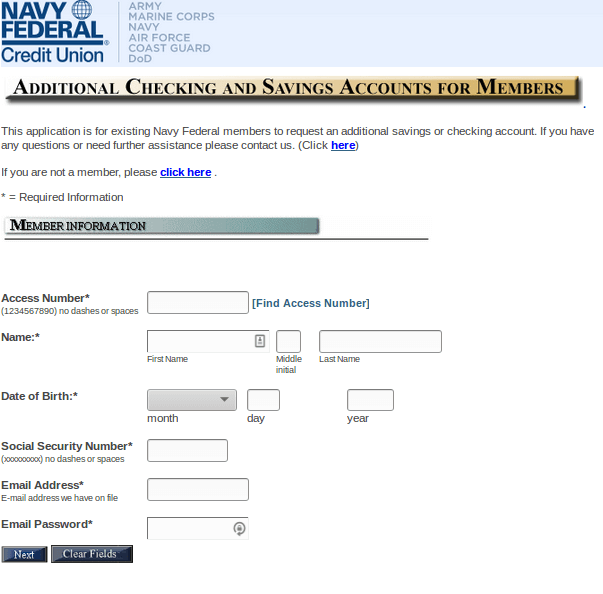
Assuming the user did not see the link before clicking and disregards the address bar, the phishing page is actually a rather convincing one. Sometimes these pages are low effort and just thrown together. Misspelled items, pictures not aligning, etc. But this one is pretty spot on to the real Navy Federal page. By phishing campaigns utilizing more convincing pages, it's likely less of the victims will be taking the proper steps of looking closer and verifying they are indeed at the right website.
Click the images below and see if at a quick glance you can spot the fake phishing site.
The phishing website is the image on the right. Minus a few alternate images and details that no user probably has memorized, as well as changing slides on a regular basis, catching any minor details that would throw a red flag is nigh impossible. Stealing the HTML formatting and files used on a website is a rather trivial task as well. The attacker may need to put in slightly more effort to get formatting and images all looking correct on a copied version, but nothing that's too much effort.
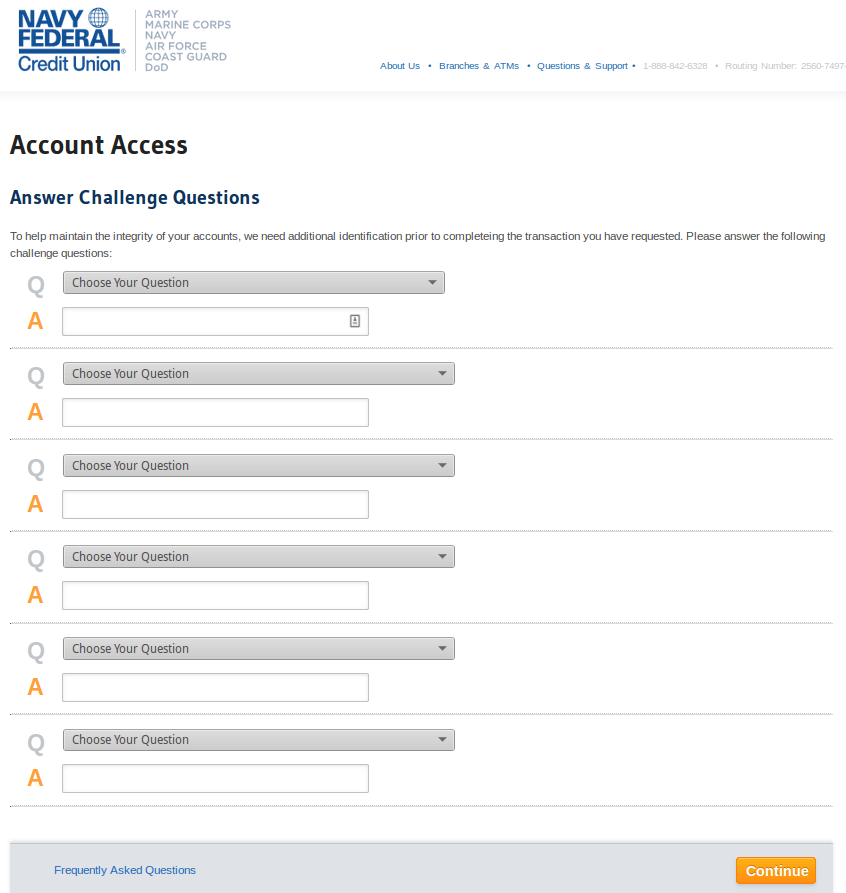
Once credentials are typed in, the server already has the login details. But from there, it brings up more pages asking for more details. This would hopefully also throw some red flags as well since this is likely very far from the normal login process. If someone were to complete all of the questions and details asked about them though, the attackers running the phishing site would hit a jackpot of data about a user. Opening opportunities for identity theft or further spearphishing campaigns. If they have things like bank account numbers and even your SSN#, that can make any further phishing emails using that data much more believable.
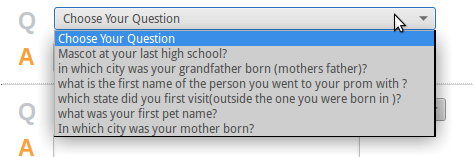
The personal questions, often used as security questions, were in two groups on the page. I assume the first question group above was different form the rest as it may be the ones they are more likely to use.
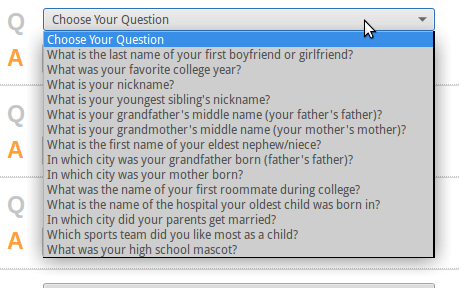
From there it goes to the hard hitting questions.
 Clicking finish will reroute you to the actual NavyFederal.org website and you be presented with a normal login page. More red flags here as going through a login process only to be rerouted to another login process is a pretty classic example of what many phishing sites do. Though it's very possible a user may just chalk it up to some generic web issue during the login.
Clicking finish will reroute you to the actual NavyFederal.org website and you be presented with a normal login page. More red flags here as going through a login process only to be rerouted to another login process is a pretty classic example of what many phishing sites do. Though it's very possible a user may just chalk it up to some generic web issue during the login.
Getting alerts or notices from banks or credit unions that are legitimate is of course a thing. So you can't really tell users to always ignore such notifications. But it's wise to advise using extra care when dealing with any banking details. Always check the URL you are at and make sure it's what you expect. Seeing an email from someone like Bank of America with a link to a .ru website is a pretty good indicator of phishing. But sometimes things aren't that easy. So taking th extra caution and time can go a long way in stopping yourself from becoming a victim.