2019 Best of Malware & Phishing "Phails"
Blog
Thought Leadership
2019 Best of Malware & Phishing "Phails"
David Pickett
MALICIOUS ATTACK "PHAILS"
While filtering over a billion messages per month, our security team constantly defends against the good, bad, and ugly of spam, malware, and phishing. There's always a steady flow of phishing and malware attempts that aren't quite the finest handiwork out there. A select few of these make it to our “phail” category. Think of these as the least sharp needles in the haystack.
Most phails are usually due to language, spelling, grammatical, or even cultural differences. These red flags are attributed to malicious actors not being familiar with the “norms” for their targets. Technical malfunctions by the sending bot or script and incorrect file paths can also result in some interesting phailed attempts.
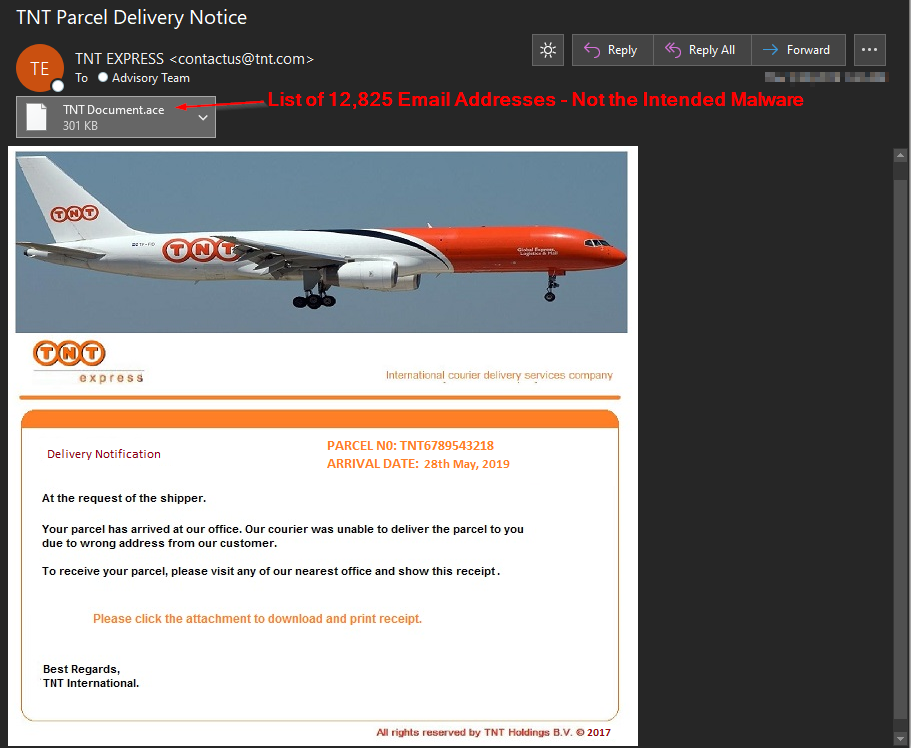
MALWARE "PHAIL"
The phail below is from an ongoing malware campaign spoofing TNT Express delivery service. These messages are normally bundled with remote access trojans or an info stealer attached. We expected to find malware inside the .ace attachment, however, it was a txt file of 12,825 email addresses instead. Most likely there was a mix-up in file paths for their recipient address lists and the malware they were supposed to be attaching. However, there wasn’t any other links or malicious payloads in these particular messages, the attackers had completely phailed for this malware attempt.
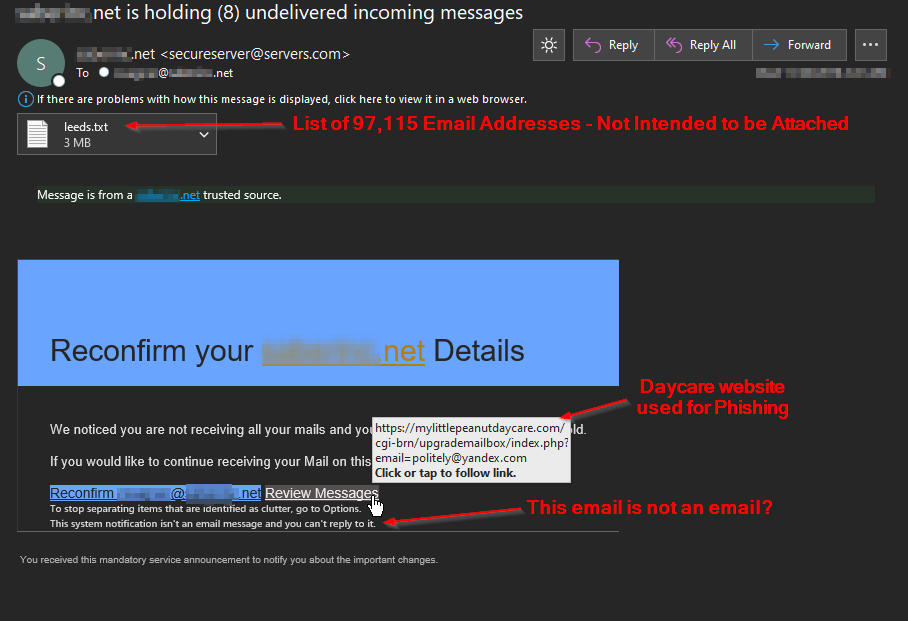
PHISHING "PHAILS"
This next phishing attempt is the star of this blog, it challenges all other attempts to surpass its phailures. Like the previous example, this one also accidentally attached their email address list (leeds.txt) of 97,115 email addresses. They took it to the next level by using a day care website to host their phishing page. To top it off, they state the email is a system notification message, not an email.
This last phishing example has phail written all over it. The phishing link pointed to a compromised bail bonds site. That's not quite as bad as a day care site above, but there's still room for improvement on where their payload could've been hosted. The wording and punctuation were the most notable offenders that should raise a red flag. It also used "Mailbox Team." as a signature and contained a copyright logo to attempt to add extra authenticity. Maybe a phishing template this bad should be copyrighted?

Contact us today for a free trial of our Advanced Email Security
